LERSSE student Yazan Boshmaf (co-supervised with Matei Ripeanu) has presented at NDSS last part of his Ph.D. research, Integro.
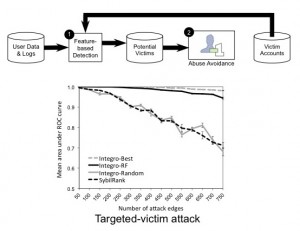
It helps OSNs detect automated fake accounts using a robust user ranking scheme. The key idea is based on an insight that victims, benign users who control real accounts and have befriended fakes, form a distinct classification category that is useful for designing robust detection mechanisms. As attackers have no control over victim accounts and cannot alter their activities, a victim account classifier which relies on user-level activities is relatively hard to circumvent. Moreover, as fakes are directly connected to victims, a fake account detection mechanism that integrates victim prediction into graph-level structures can be more robust against manipulations of the graph.Integro starts by predicting victim accounts from user-level activities. After that, it integrates these predictions into the graph as weights such that edges incident to predicted victims have lower weights than others. Finally, Integro ranks user accounts based on a modified random walk that starts from a known real account. Integro guarantees that most real accounts rank higher than fakes so that OSN operators can take actions against low-ranking fake accounts. We implemented Integro using widely-used, open-source parallel computing platforms in which it scaled nearly linearly. We evaluated Integro against SybilRank, the state-of-the-art in fake account detection, using real-world datasets and a large-scale deployment at Tuenti, the largest OSN in Spain. In particular, we show that Integro significantly outperforms SybilRank in user ranking quality, with the only requirement that the used victim classifier is better than random. Moreover, the deployment of Integro at Tuenti resulted in an order of magnitude higher fake account detection precision, as compared to SybilRank.
For more details, read the paper.